 [Image: Flocking diagram by “Canadian Arctic sovereignty: Local intervention by flocking UAVs” by Gilles Labonté].
[Image: Flocking diagram by “Canadian Arctic sovereignty: Local intervention by flocking UAVs” by Gilles Labonté].
One of many ways to bolster a nation-state’s claim to sovereignty over a remote or otherwise disputed piece of land is to perform what’s known as a “sovereignty cruise.” This means sending a ship—or fleet of ships—out to visit the site in question, thus helping to normalize the idea that it is, in fact, a governable part of that nation’s territory.
It is, in essence, a fancy—often explicitly militarized—version of use it or lose it.
Last summer, for example, Vietnam organized a private tour of the Spratly Islands, an archipelago simultaneously claimed by more than one nation and, as such, part of the much larger ongoing dispute today over who really owns and controls the South China Sea [sic].
Vietnam’s effort, Reuters reported at the time, was a strategic visit “to some of Asia’s most hotly contested islands, in a move likely to stoke its simmering dispute with Beijing over South China Sea sovereignty.”
It made “little attempt to disguise its political flavor, and comes as Vietnam pursues a bolder agenda in pushing its claims in the face of China’s own growing assertiveness.” Indeed, the cruise was apparently just the beginning, a mere “trial run ahead of Vietnam’s tentative plans to put the Spratlys on its tourism map, including scheduled passenger flights, possibly this year.”
Bring the people, in other words, and you bring evidence of governmental control.
Against this, of course, we must place the construction of entire islands by China, including the recent installation of a new primary school there, on an artificial island, a school whose opening lecture “was a geopolitical class that focused on China’s ownership of the sea.”
These sovereign games of Go taking place in disputed waters could sustain an entire blog on their own, of course, and are a topic we’ll undoubtedly return to. (Briefly, it’s worth noting that the sovereign implications of artificial islands were also part of a course I taught at Columbia a few years ago.)
Surprisingly, however, another region seen as potentially subject to future disputes over sovereignty is the Canadian Arctic. As such, arguments over such things as whether or not the Northwest Passage is an “international strait” (open to use by all, including Russian and Chinese military ships) or if it is actually a case of “internal waters” controlled exclusively by Canada (thus subject to restricted access), are still quite active.
Add to this a series of arguments over indigenous political rights as well as the specter of large-scale terrestrial transformation due to climate change, and a series of intriguing and quite complicated political scenarios are beginning to emerge there. (Who Owns The Arctic? by Michael Byers is an excellent introduction to this subject, as is Mia Bennett’s blog Cryopolitics.)
 [Image: Flocking diagram by “Canadian Arctic sovereignty: Local intervention by flocking UAVs” by Gilles Labonté].
[Image: Flocking diagram by “Canadian Arctic sovereignty: Local intervention by flocking UAVs” by Gilles Labonté].
With all this in mind, consider a fascinating report issued by Defence R&D Canada back in 2010. Called “Canadian Arctic sovereignty: Local intervention by flocking UAVs” (PDF), and written by Gilles Labonté, it opens stating that “the importance of local intervention capability for the assertion of Canadian Sovereignty in the Northwest passage is recognized.”
However, Canada presently lacks the ability to deploy at any northern position, on demand, assets that could search a wide area for rescue or surveillance purposes. This fact motivated the exploration we report here on the feasibility of a rapid intervention system based on a carrier-scouts design according to which a number of unmanned aerial vehicles (UAVs) would be transported, air launched and recovered by a larger carrier aircraft.
In other words, if Canada can’t send actual Canadians—that is, living human beings—on aerial “sovereignty cruises” by which they could effectively demonstrate real-time political control over the territories of the north, then they could at least do the next best thing: send in a flock of drones.
Doing so, Labonté suggests, would require a particular kind of flocking algorithm, one with an explicitly political goal. “In the present report,” he adds, “we propose a solution to the remaining problem of managing simultaneously the many UAVs that are required by the vastness of the areas to be surveyed, with a minimum number of human controllers and communications.”
Namely, we present algorithms for the self-organization of the deployed UAVs in the formation patterns that they would use for the tasks at hand. These would include surveillance operations during which detailed photographic or video images would be acquired of activities in a region of interest, and searching an area for persons, vehicles or ships in distress and providing a visual presence for such. Our conclusion is that the local intervention system with flocking UAVs that we propose is feasible and would provide a very valuable asset for asserting and maintaining Canadian Sovereignty in the North.
There are “formation patterns” and flocking algorithms, this suggests, that would specifically be of use in “asserting and maintaining Canadian Sovereignty in the North.”
Hidden within all this is the idea that particular flocking algorithms would be more appropriate for the task than others, lending an explicit air of political significance to specific acts of programming and computation. It also implies an interesting connection between the nation-state and behavioral algorithms, in which a series of behavioral tics might be ritually performed for their political side-effects.
For some context, the report adds, “the Canadian Government has had serious considerations of establishing a presence in the north through purchasing nuclear submarines and ice-breakers.” But why not side-step much of this expense by sending UAVs into the Arctic void instead, reinforcing nation-state sovereignty through the coordinated presence of semi-autonomous machines?
Simply re-launch your drones every two or three months, just often enough to nudge the world into recognizing your claim, not only of this remote airspace but of the vast territory it covers.
A halo of well-choreographed aerial robots flocks in the Arctic skies before disappearing again into a bunker somewhere, waiting to reemerge when the validity of the government appears under threat—a kind of machine-ritual in the open three-dimensional space of the polar north, a robotic sovereignty flight recognized around the world for its performative symbolism.
Read the rest of Labonté’s paper—which is admittedly about much more than I have discussed here—in this PDF.

 Keep your eye out for a copy of the magazine, however, because the following text is accompanied by a fold-out world map, featuring many of the sites revealed by Wikileaks.
Keep your eye out for a copy of the magazine, however, because the following text is accompanied by a fold-out world map, featuring many of the sites revealed by Wikileaks. 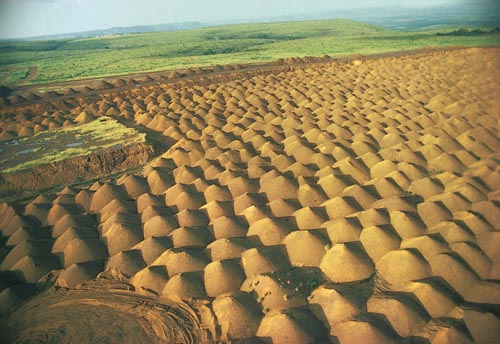 [Image: A manganese mine in Gabon, courtesy of the
[Image: A manganese mine in Gabon, courtesy of the  [Image: The Robert-Bourassa generating station, part of the
[Image: The Robert-Bourassa generating station, part of the